INTRODUCTION
The scene is mundane, almost rhythmic. You’re standing in a bustling terminal at JFK, or perhaps a quiet corner cafe in London. You reach into your pocket, pull out a small rectangle of plastic or hover your phone over a sleek black box, and wait.
Beep.
In that heartbeat, literally less than two seconds, a digital miracle has occurred. You see the word “Approved” flicker across the screen, and you go about your day. But while you were reaching for your receipt, an invisible war was fought on your behalf across three continents.
As you tapped that reader, a packet of data smaller than a grain of digital sand was fired through a labyrinth of fiber-optic cables, under oceans, and into a high-security server farm pulsing with the heat of a thousand supercomputers. There, an artificial intelligence trained on the spending habits of millions of humans, scrutinized your life. It asked: Is this really you? Or is this a thief 4,000 miles away who just bought your identity for $15 on the Dark Web?
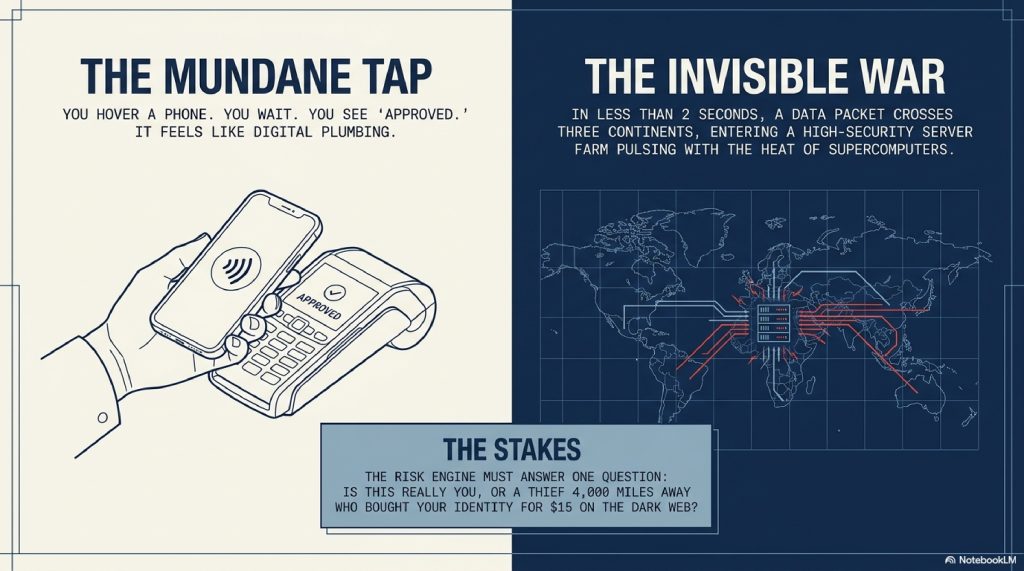
Most of us treat the “Approved” message like digital plumbing, it just works. But the reality is far more cinematic. We are currently living in the middle of a high-stakes arms race between global crime syndicates and the world’s most sophisticated algorithms. Every second, billions of dollars are at risk. If the bank’s “bouncer” is too slow, the thief escapes with the goods. If the bouncer is too aggressive, you’re left embarrassed at a dinner table with a declined card, even though you have thousands in the bank.
This is the story of the Two-Second War. It’s a journey into the “Risk Engine”, the brain of the global financial system that knows you better than you know yourself. From the way you hold your phone to the “impossible travel” algorithms that calculate the speed of a Boeing 747 in real-time, we are going to pull back the curtain on how banks catch fraudulent transactions before you even have time to put your card back in your wallet.
Welcome to the world of instant detection.
TABLE OF CONTENTS
- The Simple Explanation: The Digital Bouncer
- The 2,000-Mile Relay: Step-by-Step Breakdown
- The AI Brain: From “Rules” to “Intuition”
- Digital Fingerprints: Behavioral Biometrics
- The Advanced Layer: Behind the Infrastructure
- The “Impossible Traveler”: Real-World Examples
- Common Myths About Bank Fraud
- The Future: Quantum Threats and Federated Learning
- Fascinating Facts about Fraud Detection
- FAQs
- Conclusion
1. The Simple Explanation: The Digital Bouncer
To understand how a bank catches fraud, stop thinking about computers and start thinking about a world-class nightclub.
Imagine you are a regular at “Club Finance.” You go there every Friday, you always wear a blue jacket, you buy two drinks, and you leave at midnight. The bouncer at the door knows your face, your clothes, and your rhythm.
One night, someone who looks vaguely like you shows up at 3:00 AM wearing a tuxedo and tries to buy 50 bottles of champagne. The bouncer doesn’t need to check a manual to know something is wrong. The vibe is off. He stops the person at the door and asks for three forms of ID.
Your bank’s fraud system is that bouncer, but instead of eyes, it uses data points. It doesn’t just look at how much money you’re spending; it looks at the “vibe” of the transaction. If you usually buy groceries in Chicago and suddenly someone is buying gold bars in Dubai, the “vibe” is broken.
The Internet is the Bouncer’s Radio. It communicates with other bouncers across the world instantly to see if you’ve been spotted elsewhere.
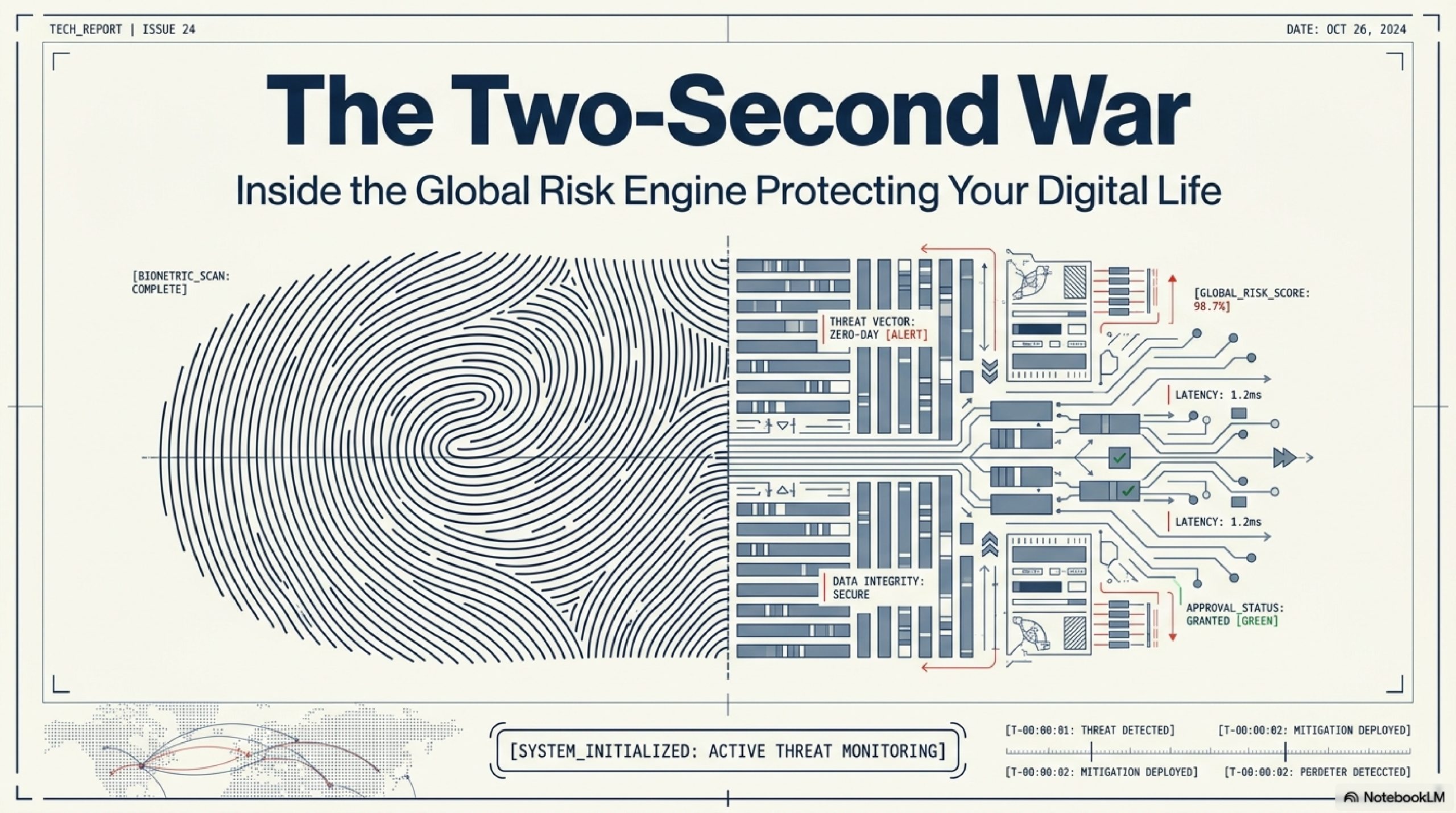
[Visual Suggestion: An illustration of a “Digital Bouncer” standing in front of a server, comparing a “Normal Transaction” (blue) with a “Suspicious Transaction” (red, glowing).]
2. The 2,000-Mile Relay: Step-by-Step Breakdown
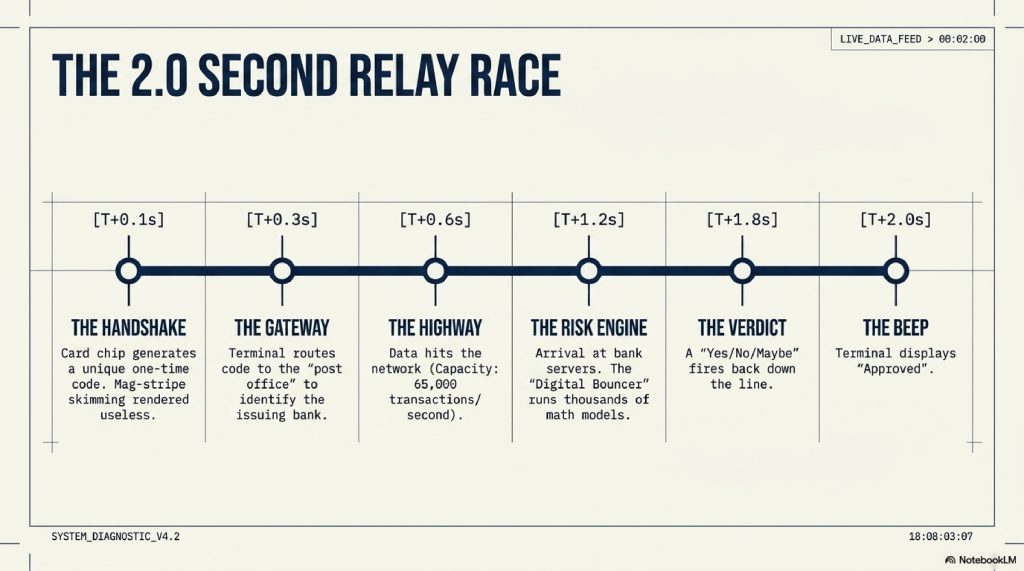
When you swipe that card, you aren’t just “paying.” You are initiating a high-speed relay race. Here is the path your data takes in those two seconds:
- Step 1: The Handshake (0.1 Seconds) The merchant’s terminal (the card reader) “talks” to your card’s chip. The chip generates a unique, one-time code. This is why “skimming” (copying the mag-stripe) is dying—the code changes every time.
- Step 2: The Gateway (0.3 Seconds) The terminal sends this code to a “Payment Gateway” (think of this as the post office). The Gateway looks at the card and says, “Aha, this is a Visa card issued by Chase.”
- Step 3: The Highway (0.6 Seconds) The data travels across the Visa or Mastercard network. These are the most powerful financial highways on Earth, capable of handling 65,000 transactions per second.
- Step 4: The Risk Engine (1.2 Seconds) The data arrives at your bank’s server. This is where the bouncer lives. The “Risk Engine” runs the transaction through thousands of mathematical models.
- Step 5: The Verdict (1.8 Seconds) The bank sends a simple “Yes” or “No” (or “Maybe”) back through the highway, through the gateway, to the terminal.
- Step 6: The “Beep” (2.0 Seconds) The terminal displays “Approved.”
3. The AI Brain: From “Rules” to “Intuition”
In the old days (the 1990s), banks used “Rule-Based Systems.” They were clumsy. A rule might be: If transaction is > $5,000 AND in a foreign country, THEN decline.
Thieves quickly learned these rules. They would spend $4,999 or stay in-country.
Today, banks use Machine Learning (ML). This is a system that doesn’t follow rules; it looks for patterns. It’s the difference between a robot following a recipe and a chef who can tell if a sauce is “off” just by the smell.
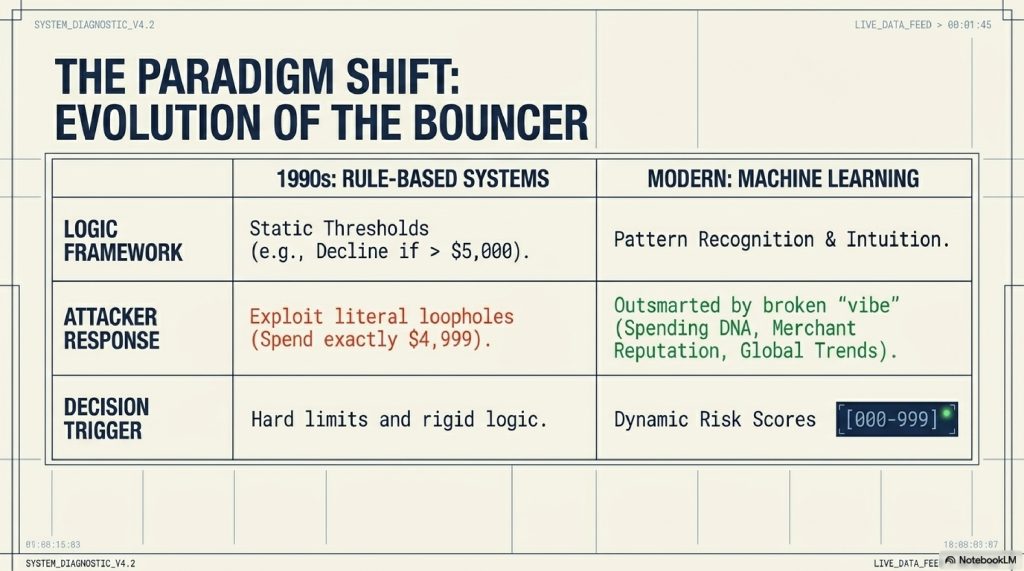
The AI looks at:
- Your Spending “DNA”: Do you always shop at Target? Do you pay your utility bills on the 1st?
- The Merchant’s Reputation: Is this a reputable store, or a shell company in a tax haven known for laundering money?
- Global Trends: Are there 500 other people currently being defrauded by this same “merchant”?
If the AI sees a pattern it doesn’t recognize, it assigns the transaction a Risk Score (usually from 0 to 999). If the score is too high, the bouncer steps in.
4. Digital Fingerprints: Behavioral Biometrics
This is where the technology moves from “smart” to “slightly eerie.” If you are shopping on your phone or computer, the bank isn’t just looking at what you are buying. It’s looking at how you move.
This is called Behavioral Biometrics.
- The Angle of the Dangle: How do you hold your phone? Everyone holds their phone at a slightly different tilt. A thief might hold it differently.
- Keystroke Dynamics: How fast do you type? What is the delay between your “S” and your “K”? You have a typing rhythm as unique as a heartbeat.
- The “Mouse” Trail: On a computer, do you move your mouse in smooth curves or jagged lines? Bots move in perfect straight lines. Humans move in messy arcs.
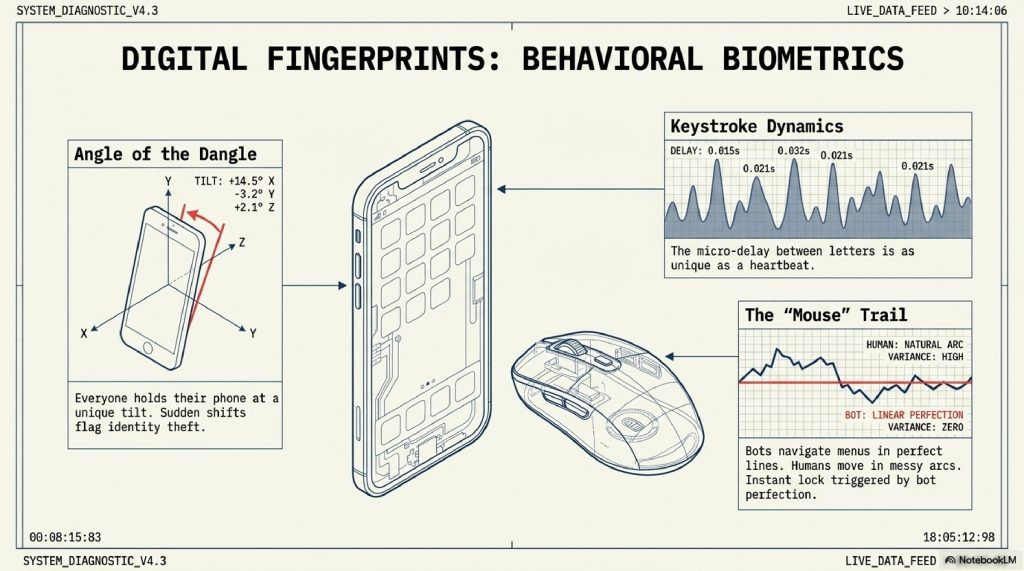
If someone steals your username and password, they might get into your account. But the moment they start “moving” inside the app, the AI realizes: “This person is moving too fast. They are navigating the menus like a robot, not like a human who’s looking for their balance.”
The result? An instant block.
5. The Advanced Layer: Behind the Infrastructure
For those who want to know the “engine specs,” the system relies on something called Neural Networks.
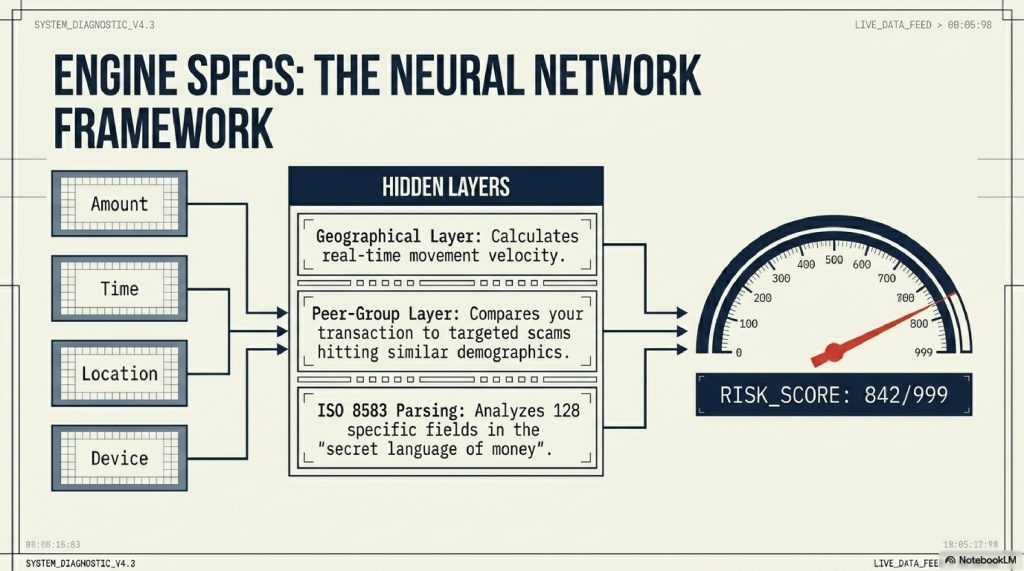
These are layers of algorithms modeled after the human brain. When a transaction arrives, it passes through “Hidden Layers” that analyze specific features:
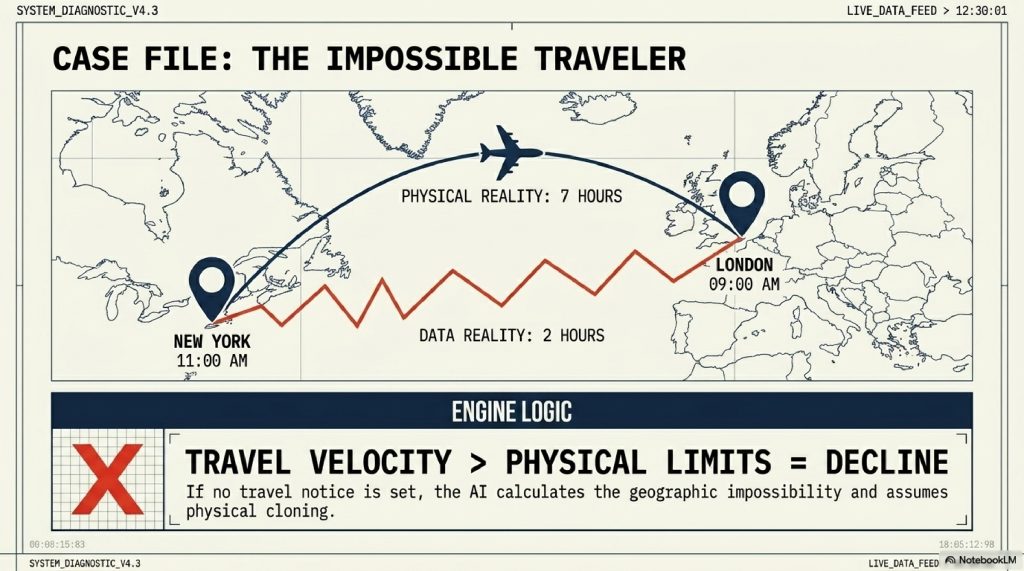
- The Geographical Layer: Calculates the “Velocity” of your movement. If you were in New York two hours ago and now your card is being used in Tokyo, the system knows no commercial plane is that fast.
- The Peer-Group Layer: Compares you to people like you. If other 30-year-olds in your zip code are suddenly being targeted by a specific “phishing” scam, your risk score goes up for those types of stores.
- The ISO 8583 Message: This is the secret language of money. It’s a standardized string of data that contains 128 different “fields.” Each field tells the bank something specific from the currency type to whether the card was physically present.
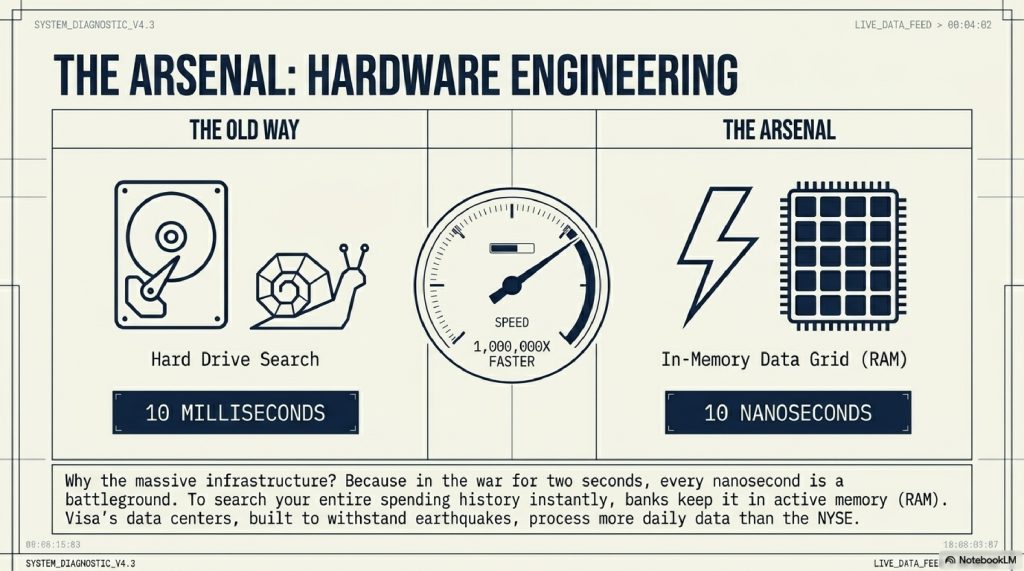
The infrastructure required to run this is immense. Banks use “In-Memory Data Grids,” which keep all of your spending history in the computer’s “active memory” (RAM) rather than on a hard drive. Why? Because searching a hard drive takes 10 milliseconds, but searching RAM takes 10 nanoseconds. In the war for two seconds, every nanosecond is a battleground.
6. The “Impossible Traveler”: Real-World Examples
Let’s look at three scenarios where the system catches a thief.
Scenario A: The Micro-Charge (The “Small Leak”)
A thief buys a list of 10,000 credit card numbers. They don’t buy a TV first. They charge $0.50 to a random charity. Why? To see if the card is active. The bank’s AI sees this “Micro-Charge” followed by a sudden jump to a $200 purchase at a gas station. This “Velocity Change” triggers an instant lock.
Scenario B: The Impossible Traveler
You buy a coffee in London at 9:00 AM. At 11:00 AM, your card is used to buy a leather jacket in New York. The system calculates that a flight from London to NYC takes 7 hours. Since only 2 hours have passed, the “Travel Velocity” is physically impossible. Declined.
Scenario C: The “New Device” Trap
You always use an iPhone 15. Suddenly, a login occurs on a Linux-based computer using a VPN (Virtual Private Network) that makes it look like it’s in the Netherlands. The AI sees that this device has never been associated with you and that the “typing speed” of the password was “instant” (meaning it was copy-pasted by a bot). Step-up Authentication (SMS code) triggered.
7. Common Myths About Bank Fraud
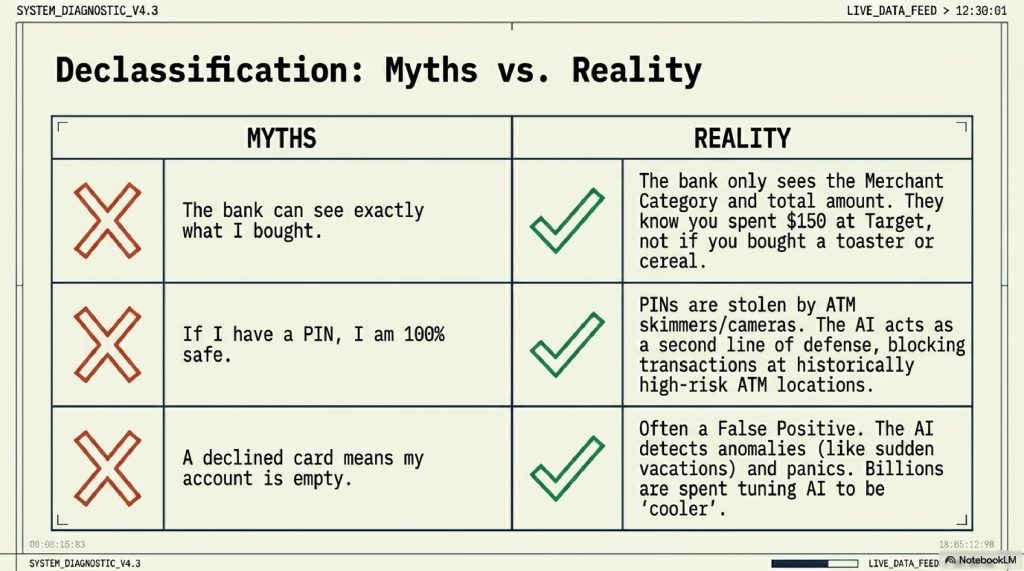
Myth 1: “The bank can see exactly what I bought.” Reality: Most of the time, the bank only knows the Merchant Category. They know you spent $150 at “Target,” but they don’t know if you bought a toaster or 50 boxes of cereal. Fraud detection is based on the store and the amount, not your specific shopping list.
Myth 2: “If I have a PIN, I’m 100% safe.” Reality: PINs can be seen by hidden cameras at ATMs or “skimmers.” The AI is actually your second line of defense. Even if a thief has your PIN, the AI might block the transaction if the ATM is in a “high-risk” area where you’ve never been.
Myth 3: “Decline means there is no money in my account.” Reality: A “Declined” message is often a False Positive. This happens when the AI gets over-excited. It sees you’re on vacation and panics. This costs banks billions in lost revenue, which is why they are constantly trying to make the AI “cooler” and less prone to panicking.
8. The Future: Quantum Threats and Federated Learning
The bouncers are getting smarter, but so are the thieves.
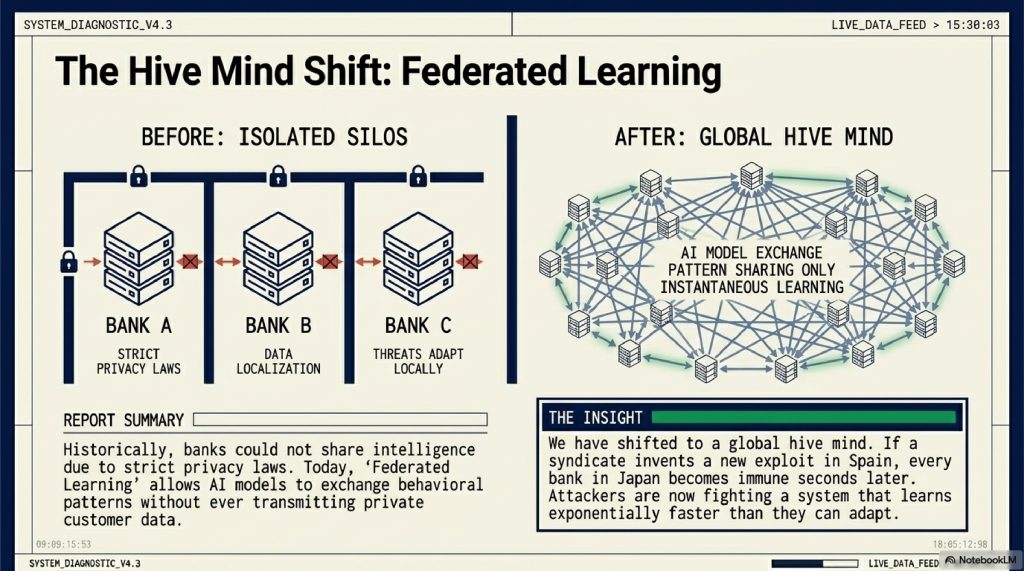
- Federated Learning: In the past, Bank A couldn’t share data with Bank B because of privacy. Now, they use “Federated Learning,” where the AI models share what they’ve learned without ever sharing your private data. If a thief develops a new trick in Spain, every bank in the world can “learn” the pattern instantly.
- Quantum Computing: Within 10 years, quantum computers might be able to crack the encryption that protects your card. Banks are already developing “Post-Quantum Cryptography” to stay one step ahead.
- The End of Cards: Soon, your “card” will just be your face or your palm. Biometric payments remove the “plastic” vulnerability entirely, moving the fight purely into the realm of identity.
9. Fascinating Facts about Fraud Detection
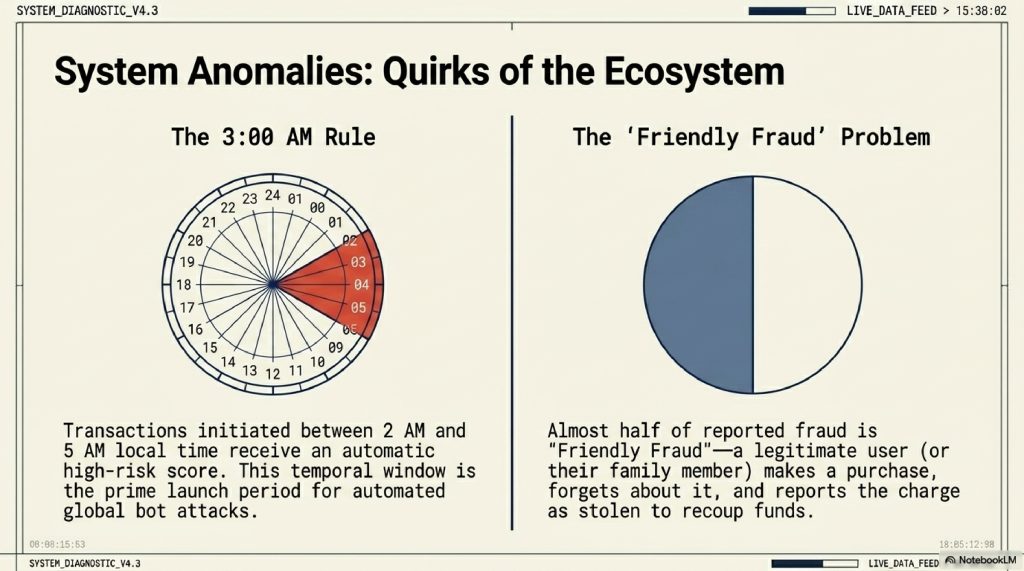
- The “Friendly Fraud” Problem: Almost 50% of “fraud” reported is actually “Friendly Fraud” where a person makes a purchase (or their kid does) and then forgets and reports it as stolen to get their money back.
- The 3:00 AM Rule: Transactions made between 2:00 AM and 5:00 AM local time have a significantly higher risk score by default. Why? Because that’s when most fraudulent “bot” attacks are launched.
- The Power of One Dollar: Many thieves “validate” cards by charging exactly $1.00. This is such a common pattern that many banks have a specific AI sub-routine just to watch for “one-buck pings.”
- Visa’s Brain: Visa’s data center is built to withstand earthquakes and has its own power grid. It processes more data in a day than the entire New York Stock Exchange.
9. FAQs
Q1: Why does my bank block my card when I travel? A: Because your “Geographic Pattern” has been broken. If you haven’t set a “Travel Notice,” the AI assumes your card was cloned by a thief in that new country.
Q2: Can a thief use my card if they have my phone? A: It’s harder. With Apple Pay or Google Pay, they need your FaceID or Fingerprint. These are much harder to “spoof” than a plastic card.
Q3: How do I know if a text from my bank is real? A: Banks will never ask for your password or PIN via text. A real fraud alert will usually just ask you to reply “YES” or “NO” to a specific transaction.
Q4: Is it safer to use a Credit Card or a Debit Card? A: Credit cards are safer. If a credit card is defrauded, it’s the bank’s money that is missing. If a debit card is hit, it’s your rent money that is gone. Credit cards also have better legal protections for consumers.
Q5: What is “Card Not Present” fraud? A: This is fraud that happens online or over the phone, where the physical card isn’t used. This is currently the fastest-growing type of fraud.
Q6: Does the “Zip Code” check at gas stations actually work? A: Yes. It’s a simple “Athentication Layer.” If a thief steals your card number but doesn’t know your home zip code, they can’t buy gas, which is often the first thing they try to do.
Q7: How long does it take to get my money back after fraud? A: Usually, the bank will issue a “Provisional Credit” within 24–48 hours while they investigate.
Q8: Can AI detect “Deepfake” voices used for phone banking? A: Banks are now using “Voice Biometrics” that look for the “spectral signature” of a human throat. AI-generated voices often lack these subtle biological imperfections.
Q9: Why does the bank ask me to “Identify the pictures with traffic lights”? A: This is a CAPTCHA. It’s designed to stop “Brute Force” attacks where a bot tries 1,000 passwords a second.
Q10: What is the most common way cards are stolen today? A: Phishing. Not high-tech hacking, but a simple email or text that tricks you into typing your card info into a fake website.
10. INTERNAL LINKING SUGGESTIONS
- How Do VPNs Work? The Complete Guide to Virtual Private Networks
- How GPS Works: The Science of Satellites and Location
- Why Public Wi-Fi is Dangerous: The Invisible Risks Explained
11. CONCLUSION
In the two seconds it took you to read this sentence, the global financial system just caught three thousand thieves.
We often feel like technology is making our lives more vulnerable, and in some ways, that’s true. The digital world is full of shadows. But for every thief trying to find a crack in the door, there is a brilliant, tireless “Digital Bouncer” standing guard.
The miracle of the modern bank isn’t just that it holds your money; it’s that it knows you. It knows your rhythm, your habits, and your “vibe.” It’s a system built on the most advanced science our species has ever created, all so that you can stand in a coffee shop, tap a piece of plastic, and hear that reassuring beep.
The Two-Second War is a war being won by the good guys. And while the thieves will keep getting smarter, the AI is a student that never sleeps. So, the next time you see “Approved” on a screen, give a silent thanks to the bouncer in the machine. Your money is safe not because the doors are locked, but because the bouncer is watching the room.
Comment