INTRODUCTION The red bar. It is the universal symbol of 21st-century anxiety. When that tiny sliver of light on your smartphone turns from white to crimson, your behavior changes. You dim your screen, you close your background apps, and you begin a desperate, subconscious hunt for a wall outlet. We…
Category: CyberSecurity
Navigate the rapidly evolving 2026 threat landscape. Discover expert insights on defending against Agentic AI attacks, implementing Zero Trust architectures, and preparing for the post-quantum cryptography era. Protect your infrastructure from deepfakes, cross-domain breaches, and supply chain vulnerabilities.
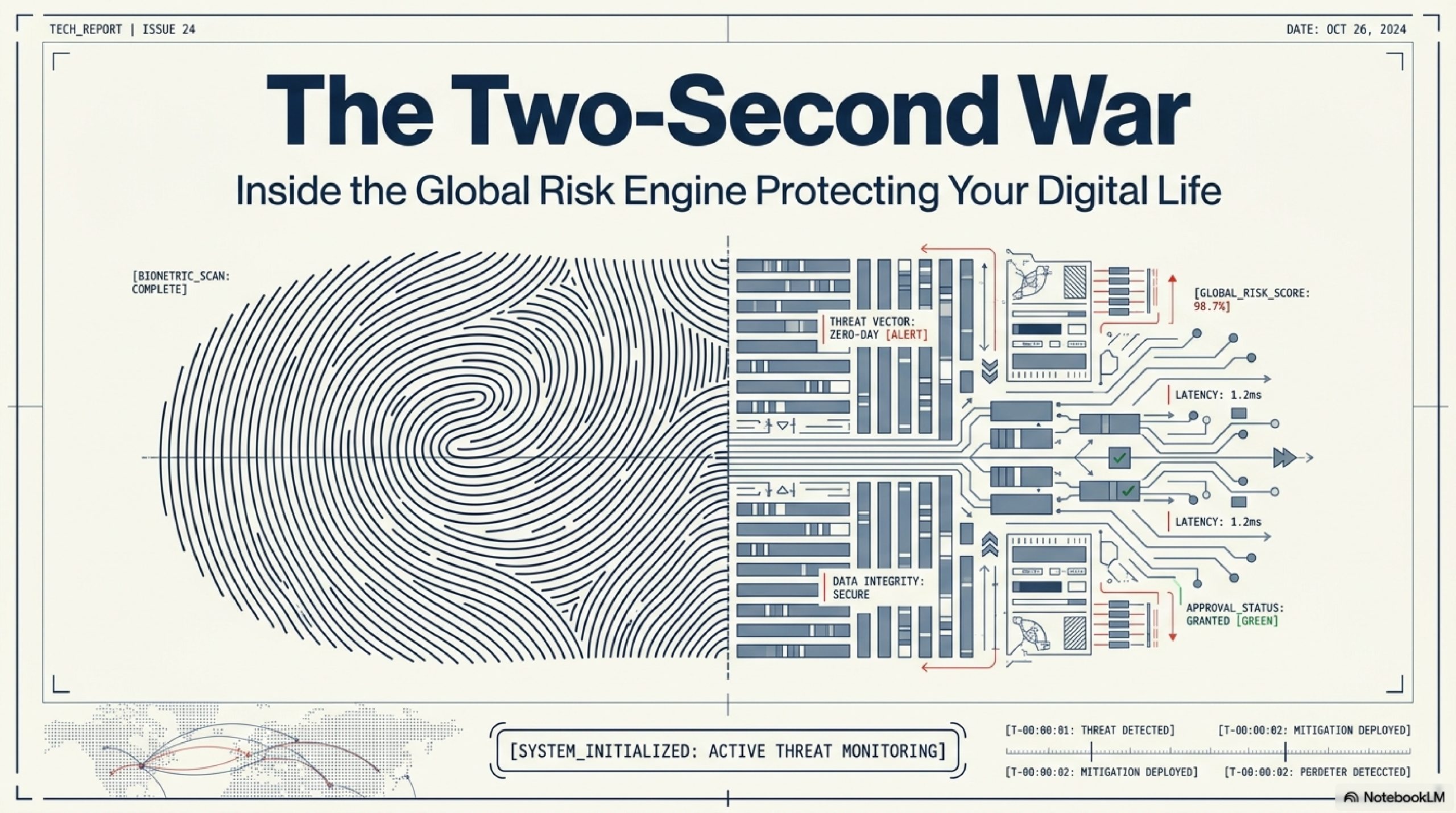
How Banks Catch Fraudulent Transactions in Seconds
INTRODUCTION The scene is mundane, almost rhythmic. You’re standing in a bustling terminal at JFK, or perhaps a quiet corner cafe in London. You reach into your pocket, pull out a small rectangle of plastic or hover your phone over a sleek black box, and wait. Beep. In that heartbeat,…
Why Public Wi-Fi is Dangerous: The Invisible Risks Explained
INTRODUCTION The scene is familiar, almost comforting. You walk into a bustling airport terminal, stressed by a layover, or settle into a corner chair at a local coffee shop. Your phone vibrates. A notification appears: “Free Public Wi-Fi Available.” With a quick tap, you’re connected. You check your bank balance,…
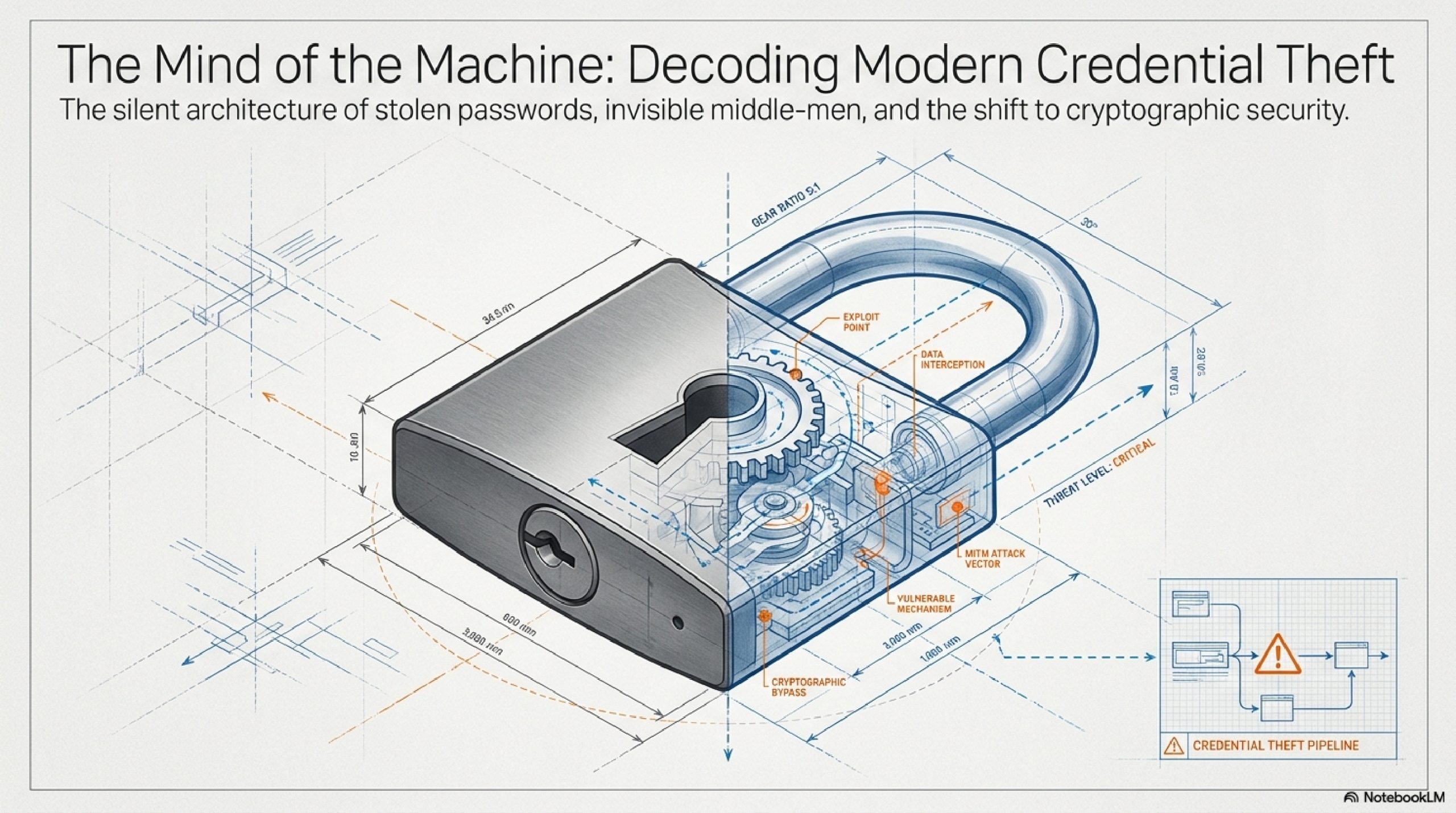
How Hackers Steal Passwords Without You Realizing
INTRODUCTION It is 8:30 AM on a Tuesday. You are sitting at a coffee shop, sipping a latte, scrolling through your morning emails. An alert pops up on your phone: “Unusual login attempt from Moscow, Russia. Please verify your account.” There is a helpful link right below the message. You…
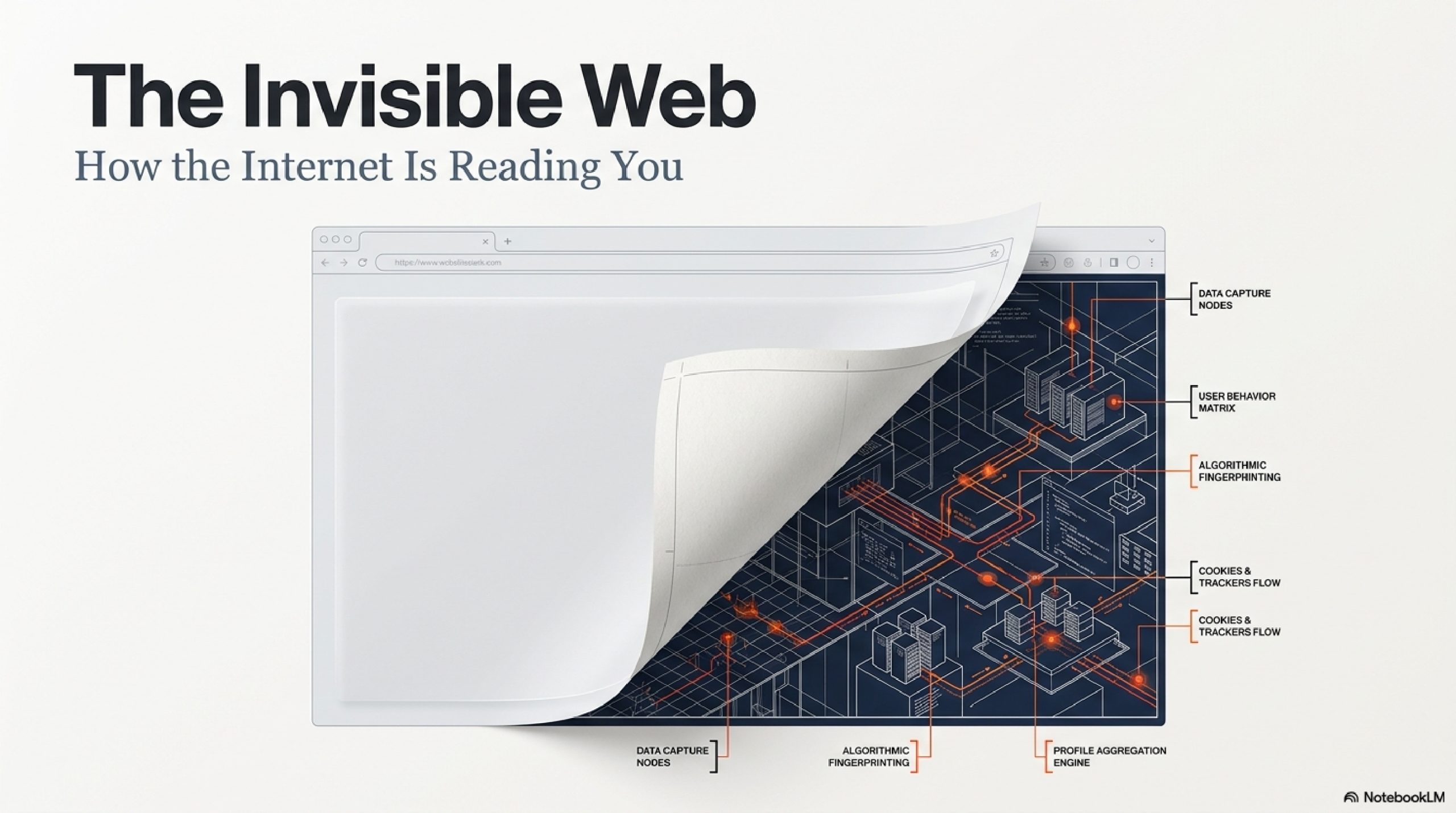
How Websites Track You Across the Internet (Explained Simply)
INTRODUCTION You know the feeling. You are sitting on your couch, browsing the web on your phone. You briefly search for a pair of blue running shoes. You click on a website, scroll for ten seconds, decide they are too expensive, and close the tab. You don’t create an account….